Data Breaches Rampant in 2008
More electronic records were breached in 2008 than the previous four years combined, according to the 2009 Verizon Business Data Breach Investigations Report (pdf) released this Wednesday.
The research is based on Verizo
Key findings from Verizon's report:
- Most data breaches investigated were caused by external sources. External data breaches are highest in Eastern Europe, East Asia and North America; these regions combined account for 82% of all external attacks.
- Most breaches (64%) resulted from a combination of events rather than a single action. For example, an attacker exploiting a mistake committed by the victim, hacking into the network, and installing malware on a system to collect data.
- In 69% of cases, the breach was discovered by third parties - most organizations do not discover their own breaches.
- Nearly all records compromised in 2008 were from online assets, but not desktops, mobile devices, portable media, etc. Rather, 99% of all breached records were compromised from servers and applications.
- Roughly 20% of 2008 cases involved more than one breach.
- "Highly sophisticated" attacks account for only 17% of breaches, Verizon said. Still, these cases accounted for 95% of the total records breached, which indicates that hackers know where and what to target.
- Being Payment Card Industry (PCI) -compliant is critically important: 81% of affected organizations subject to the Payment Card Industry Data Security Standard (PCI-DSS) had been found non-compliant prior to being breached.
Data breaches investigated in 2008 affected a wide array of organizations:
- Food and beverage establishments, the second most frequently hit industry in the first report, dropped to 14% in 2008, down from 20%.
- The retail industry accounts for a third of all cases.
- Breaches in the financial services increased the most, doubling to a share of 30%, and representing 93% of the compromised records in the study - with 90% of these records involving groups engaged in organized crime.
Mistakes and oversight failures - as opposed to lack of resources and hindered security efforts - were identified as the main cause of the breaches. And 90% of all breaches could have been avoided if basic security guidelines had been followed, Verizon concluded from a previous study, covering 230 million compromised records from 2004 to 2007.
These are: changing default credentials; avoiding shared credentials; reviewing user accounts; employing application testing and code review; patching comprehensively; assuring HR uses effective termination procedures; enabling application logs and monitoring them; and defining "suspicious" and "anomalous" - be prepared to defend against and detect very determined, well-funded, skilled and targeted attacks.
Cybercrime is always evolving, Verizon said.
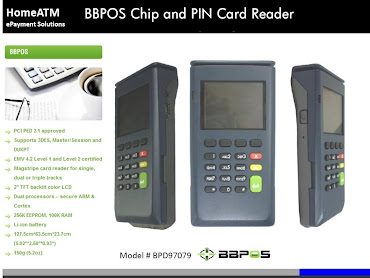
For example, new methodologies, like memory scraping malware, are being used to steal personal identification codes, or PIN numbers, associated with credit/debit accounts, to withdraw cash directly from a consumer's account.








0 comments