 Last week in a post entitled: "Got Hacked? Bank on It" I talked about webjacking and made a prognostication that these types of hacks will milk your hard drive for information and become more common in 2009.
Last week in a post entitled: "Got Hacked? Bank on It" I talked about webjacking and made a prognostication that these types of hacks will milk your hard drive for information and become more common in 2009. "I'm sorry to report that it doesn't look like this will be the last time this year...I'll be talking about webjacking ...these webjack attacks will become almost as common as a Gulf of Aden pirate attack."
Well, it didn't take long for a webjacking to make "news."
The bad news is, IT IS THE NEWS.
Using mainstream news headlines regarding recent events in Gaza, it lures people to a site that apprears to be CNN. The bad news is, it isn't CNN...it's a clone, and you there is nothing which clearly indicates that you've been duped.
This email spam attack contains "headline" news links to a website masquerading as CNN. Once there, user's are innocuously instructed to download an Adobe Acrobat 10 update, which, instead, infects the user’s computer with a password-stealing Trojan virus which scrapes the hard disk looking for banks/financial service data.
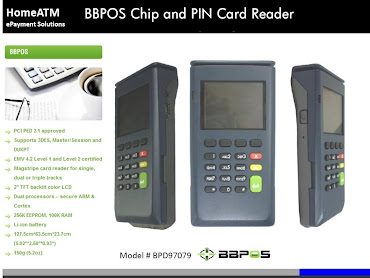
This is a disconcerting development to say the least, and I've got some "ews" for you. If you EVER type in your credit/deibt PAN (Personal Account Number) or PIN into a browser space that's "your bad." The "good news" is that you can protect yourself with your own personal swiping device from HomeATM.
Here's the story from ComputerWorld:
Hackers have launched a large-scale spam attack masquerading as CNN.com news notifications about the Israeli invasion of Gaza, security researchers said today, in a repeat of a massive campaign last summer that also posed as CNN alerts.
Yesterday morning, RSA's FraudAction Research Lab spotted the first messages in the new attack, which take advantage of the ongoing conflict in Gaza. Israeli ground forces entered Gaza on Jan. 3 after several days of airstrikes and naval bombardments that began Dec. 27.
The messages, said Sam Curry, vice president of product management at RSA, pose as alerts from the CNN cable news channel, and promise "graphic and striking" images about the conflict in Gaza between Israel and Hamas.
"It starts off with phishing e-mail that tries to look like CNN," said Curry, "and then the social engineering aspect kicks in. The message tries to get you to go to a Web site that looks like CNN.com. There, the [fake] site says you must update to Adobe Acrobat 10." Accepting the download delivers a Trojan horse to the PC instead.
"The Trojan is an 'SSL' stealer," added Curry. "It scrapes the disk and looks for traffic to and from known financial services."
The attack had been prepared weeks in advance, said Curry, and the hackers had only decided in the last several days to hang it on the events in Gaza. The FraudAction Research Labs' usual monitoring of cybercriminal activity, he said, had uncovered talk about an impending attack as much as four weeks ago.
During the interval, the attacks bandied ideas about what current event they would use to bait their attack. "There was some talk about the inaugural [of Barack Obama next week], the economy and massive drops in the Dow," Curry said. "They talked about how the news had to hit a critical threshold."
They eventually selected news of the Israeli attacks in Gaza against Hamas. "The thing is that they're completely apolitical," Curry noted. "They were ready to exploit significant news either way, whether there was a cease fire or an intensification of the conflict... (continue reading at ComputerWorld)








0 comments