In fairness to Heartland Payment Systems, I want to add this addendum to my previous post. Unlike CardSystems, which PBT bought after their 40 million card breach, Heartland was PCI certified.
Then again, so was Hannaford at the retail level. So what does this mean? Since hackers have shifted their attention from retailers to, at least in this case, acquirers, where does it end? It doesn't end here, that's for sure.
I'll tell you where it ends...it "ends at the beginning", and the "beginning of the end" of a transaction is at the Visa/MC network level.
Therefore, Visa/MC and their PCI, which has cost retailers and processors over $2 billion dollars to implement...needs to take some of the blame. Heartland played by "their rules." The hackers were the ones that breached them. So who's really to blame? Sure the hackers would be the first answer, but second to none is Visa/MC.
 After all, if you need to "unencrypt" encrypted information, which is where the HPS breach occurred, and it took 4+ months for Visa/MC to determine suspicious activity, then maybe the hackers have gotten to the Point of No Return.
After all, if you need to "unencrypt" encrypted information, which is where the HPS breach occurred, and it took 4+ months for Visa/MC to determine suspicious activity, then maybe the hackers have gotten to the Point of No Return.The "Mother of All Hacks" will never be Heartland Payment Systems. It will be the electronic payments system at it's very core. Whether it's Visa, MasterCard or NACHA, if any of these systems are breached, it's the end of e-payments as we know it. Do they know it?
With TJ Max, it was the retailers fault (storage), with CardSystems, it was non PCI compliance. (Also storage anomalies) but with Heartland, where does the fault lie? Can it be a PCI certified acquirer's fault? They complied...yet they are going to take the fall. I say that unless new information comes forward...they shouldn't.
With TJ Max, it was the retailers fault (storage), with CardSystems, it was non PCI compliance. (Also storage anomalies) but with Heartland, where does the fault lie? Can it be a PCI certified acquirer's fault? They complied...yet they are going to take the fall. I say that unless new information comes forward...they shouldn't.
So the way I see it, PCI, not Heartland has been breached. And not for the first time.
Hackers may very well have gotten to the very "core" of payment transaction platforms...the point where encrypted info needs to be "unencryped" in order to complete authorization. I'm no security expert, but what good is encryption if it needs to be "unencrypted"...at ANY point in the process?
Does V/MC think their systems are beyond attack? If I was a hacker and I knew the weak point was where unencryption occurs, then it "occurs" to me that point should be the must vulnerable point of attack.
What if ,as I stated in a previous posts the bad guys (darkhats) Ireally know more than the good guys? (the whitehats) Then, is all the money spent to protect data at the "point of sale" morphing into a "point of no returrn" on the investment. If so, what's the point?
In God we Trust...but what about Visa/MC?
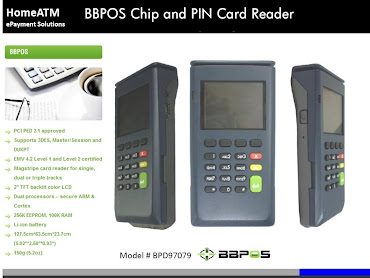
Want to "charge" something? Then use Visa/MasterCard. For secure payments, I'll continue to put my faith in the Debit/ATM networks. Heartland admitted, that although all the information on the magnetic stripe was hacked, no PIN's were. That seems to be something the hacker's can't quite PIN down.
PIN Debit Payments Blog








0 comments