Top Online Retail Categories
Source: Practical eCommerce
According to a report by Nielson Online, the Top Online Retail Categories were led by Event and movie tickets, which earned average orders of $252.14 in March 2009
The report from Nielsen Online via MarketingCharts.comshowed that the ticket category outpaced its closest competitorcategory, computer hardware, by more than $63 per average order.
Automotive-related products and consumer electronics each generatedslightly more than $120 on a typical order, while child and baby careitems, sporting goods, home and garden products, office supplies, andfood products all hovered near $75 in revenue for a customary order.
All Top Banking
Minneapolis, Apr. 27, 2009 -- Digital River, Inc. (NASDAQ: DRIV - News), a leading provider of global e-commerce solutions, announced that it is significantly expanding its relationship with Eastman Kodak Company to manage Kodak’s global e-commerce operations. Under the agreement, Digital River will be providing a full range of e-commerce and e-marketing services to support all consumer online sales of Kodak’s innovative line of digital cameras, digital video cameras, digital picture frames, all-in-one inkjet printers, film and accessories across multiple countries in North America and Europe.
“Conducting cross-border e-commerce is a complex proposition involving multiple languages and currencies, banking relationships, international regulations, taxes and more,” said Joel Ronning, Digital River’s CEO. “Digital River has the global footprint, infrastructure and e-commerce expertise to help companies cut through this complexity and successfully enter online markets much faster and with less risk than they can on their own. We are pleased to expand our relationship with Kodak and work with them in delivering their world-class brand and products to customers around the globe.”
In addition to the new global agreement, Digital River currently manages business-to-business e-commerce sites for Kodak’s Document Imaging and Print on Demand Solutions groups.
About Kodak
As the world’s foremost imaging innovator, Kodak helps consumers, businesses, and creative professionals unleash the power of pictures and printing to enrich their lives. To learn more, visit http://www.kodak.com and follow our blogs and more at http://www.kodak.com/go/followus .
About Digital River, Inc.
Digital River, Inc., a leading provider of global e-commerce solutions, builds and manages online businesses for software and game publishers, consumer electronics manufacturers, distributors, online retailers and affiliates. Its multi-channel e-commerce solution, which supports both direct and indirect sales, is designed to help companies of all sizes maximize online revenues as well as reduce the costs and risks of running an e-commerce operation. The company’s comprehensive platform offers site development and hosting, order management, fraud management, export controls, tax management, physical and digital product fulfillment, multi-lingual customer service, advanced reporting and strategic marketing services.
Founded in 1994, Digital River is headquartered in Minneapolis with offices across the U.S. as well as Brazil, China, England, Germany, Ireland, Japan, Luxembourg and Taiwan. For more details about Digital River, visit the corporate Web site at www.digitalriver.com or call 952-253-1234.
Source: Company press release.

Click the Links Below to Learn More:
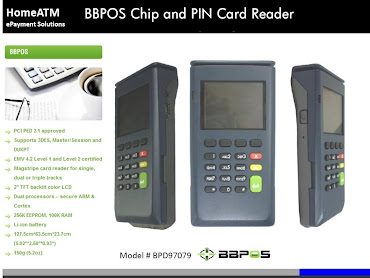
- More About HomeATM's PCI 2.0 PIN Entry Device Certification
- More About HomeATM's Person to Person Money Transfer
- More About HomeATM's Two-Factor Authentication for Online Banking
- Are You an ISO? Click Here to Read About Our ISO Distribution Platform
- Click Here to Read our White Paper
Source: CBR
Yahoo profit plunges 78% in weak Q1
Published:27-April-2009
By Datamonitor staff writer
Plans to cut its workforce by 5%
Yahoo has reported a 78% decline in net income at $118m for the first quarter 2009, compared to $537m in the year-ago quarter, on revenue down 13% at $1.6 billion. It said it plans to cut its workforce by 5% after profit was hit by currency rate fluctuations, the sale of Kelkoo, and lower revenue from broadband partnerships, voice-over IP services, and subscription music offerings.
During the quarter, operating income declined 17% to $101m, while diluted EPS fell 80% to $0.08, compared to $0.37 in the first quarter of 2008.
Marketing services revenue declined 12% to $1.38 billion, with owned and operated sites revenue decreasing 10% to $872m and affiliate sites revenue decreasing 16% to $511m. Fees revenue fell 20% to $197m. Geographically, US revenue declined 9% to $1.2 billion, while international revenue fell 23% to $392m.
Source: spamfighter
Complete item: http://www.spamfighter.com/News-12258-Malware-Compelled-Franklin-Savings-Bank-to-Shutdown-Website.htm
Description:
The Franklin Savings Bank (Farmington, USA), which shutdown its marketing site for the 2nd time in a week, put online customers at inconvenience. (See picture on left...we've got security AND convenience)
However, early detection proved helpful in preventing a malware from spreading.
On April 9, 2009, customers could not access the bank's site, as the bank took it offline following the malware's detection by their security mechanisms. The problem appeared again on April 15, 2009, resulting in another shutdown till the bank shifted site to some other Web host.
Presently, consumers attempting to visit Franklin Savings Bank's websites, www.franklinebranch.com, www.westernmountainfinancial.com and www.fsbme.com would find a warning that says these websites are not available because of system maintenance.
Tim Thompson, Senior Vice President, Franklin Savings Bank, said that the malware that attacked their web page in the 2nd week of April 2009 seemed to be spreading widely on the PC servers belonging to the web hosting firm, as reported by sunjournal on April 17, 2009.
Thompson further said that they blocked access to the page again so that the threat did not reach their clients. According to him, the bank was shifting to a new hosting firm and soon they would have a new page for its visitors.
Meanwhile, authorities stated that client data was safe as the affected website was not linked to the bank's operations. They also said that it was essential to know that the bank's marketing website was separate from the software for online banking and it did not have any link with customer information.
E-Secure-IT
https://www.e-secure-it.com
Complete item: http://www.spamfighter.com/News-12258-Malware-Compelled-Franklin-Savings-Bank-to-Shutdown-Website.htm
Description:
The Franklin Savings Bank (Farmington, USA), which shutdown its marketing site for the 2nd time in a week, put online customers at inconvenience. (See picture on left...we've got security AND convenience)
However, early detection proved helpful in preventing a malware from spreading.
On April 9, 2009, customers could not access the bank's site, as the bank took it offline following the malware's detection by their security mechanisms. The problem appeared again on April 15, 2009, resulting in another shutdown till the bank shifted site to some other Web host.
Presently, consumers attempting to visit Franklin Savings Bank's websites, www.franklinebranch.com, www.westernmountainfinancial.com and www.fsbme.com would find a warning that says these websites are not available because of system maintenance.
Tim Thompson, Senior Vice President, Franklin Savings Bank, said that the malware that attacked their web page in the 2nd week of April 2009 seemed to be spreading widely on the PC servers belonging to the web hosting firm, as reported by sunjournal on April 17, 2009.
Thompson further said that they blocked access to the page again so that the threat did not reach their clients. According to him, the bank was shifting to a new hosting firm and soon they would have a new page for its visitors.
Meanwhile, authorities stated that client data was safe as the affected website was not linked to the bank's operations. They also said that it was essential to know that the bank's marketing website was separate from the software for online banking and it did not have any link with customer information.
E-Secure-IT
https://www.e-secure-it.com
US Online Sales Up
Source: eMarketer
APRIL 27, 2009
In dark days, e-commerce shines.
Most US economic indicators were down in Q1 2009, but online sales were an exception.
According to a survey by Forrester Research and Shop.org, US online retail sales rose an average of 11% in the first three months of 2009.
Of the 80 companies studied, 58% saw online sales increases compared with the same quarter last year.
Looking further into the findings, 44% of the e-tailers reportedincreases of over 10%, 14% showed increases up to 10% and 13% reportedflat sales.
“It seems that consumer confidence is getting better,”Sucharita Mulpuru, a Forrester analyst, told Bloomberg News. “Hopefullythe worst is behind us.”
Looking ahead, Citi Investment Research projects that US retail e-commerce sales will grow 4.4% in 2009 to $141 billion—and jump to 16.5% growth in 2010.
Could happy days be here—at least online—again? Maybe not for Web-only retailers.
- Banking / Finance News
Source: Finextra
Complete item: http://www.finextra.com/fullstory.asp?id=19965
Description:
A former IT worker at the Federal Reserve Bank of New York (FRB-NY) and his brother have been arrested for allegedly stealing the personal information of bank employees and using it to obtain loans.
Curtis Wiltshire worked as an information and technical analyst at the Federal Reserve Bank of New York in lower Manhattan, providing him with access to information about other employees, including names, dates of birth, social security numbers and photographs.
E-Secure-IT
https://www.e-secure-it.com
Source: Finextra
Complete item: http://www.finextra.com/fullstory.asp?id=19965
Description:
A former IT worker at the Federal Reserve Bank of New York (FRB-NY) and his brother have been arrested for allegedly stealing the personal information of bank employees and using it to obtain loans.
Curtis Wiltshire worked as an information and technical analyst at the Federal Reserve Bank of New York in lower Manhattan, providing him with access to information about other employees, including names, dates of birth, social security numbers and photographs.
E-Secure-IT
https://www.e-secure-it.com
Banking/Finance - ATM / POS
Source: ABC News
Complete item: http://abcnews.go.com/Technology/Business/story?id=7434509&page=1
Description:
Sean Seibel thought it looked just like any other ATM -- at least at first.
Earlier this month, the 33-year-old Microsoft employee, who lives in New York City, stopped in the closest Chase bank to get some cash to pay his barber. But when he inserted his ATM (automatic teller machine) card in the machine, he noticed a bit of resistance.
The screen said the machine was unable to read his card. So he tried again. But a second time, the machine gave him an error message.
He was about to give up and try another machine, when a thought popped into his head. He had heard about devices that fraudsters attach to the outside of card readers on ATM machines and, though it seemed unlikely, wondered if that was the source of his problem.
"I'm looking at the thing and thinking this can't be - no way," he said. "There are all these stories and myths about it, but I actually found one in the wild."
With a combination of fear and exhilaration, he tried to pull on the green plastic surrounding the card slot and found that it peeled right off.
Three Skimmers Found in One Week
But that same week Nick McGlynn, a 26-year-old photographer, also spotted an ATM skimmer at a different Chase bank in New York City. He had just read about Seibel's experience on a technology blog, when he walked by a set of Chase ATMs that looked peculiar.
"From the window, I could see a mirror centered on one ATM but no mirror on another," he said.
E-Secure-IT
https://www.e-secure-it.com
Source: ABC News
Complete item: http://abcnews.go.com/Technology/Business/story?id=7434509&page=1
Description:
Sean Seibel thought it looked just like any other ATM -- at least at first.
Earlier this month, the 33-year-old Microsoft employee, who lives in New York City, stopped in the closest Chase bank to get some cash to pay his barber. But when he inserted his ATM (automatic teller machine) card in the machine, he noticed a bit of resistance.
The screen said the machine was unable to read his card. So he tried again. But a second time, the machine gave him an error message.
He was about to give up and try another machine, when a thought popped into his head. He had heard about devices that fraudsters attach to the outside of card readers on ATM machines and, though it seemed unlikely, wondered if that was the source of his problem.
"I'm looking at the thing and thinking this can't be - no way," he said. "There are all these stories and myths about it, but I actually found one in the wild."
With a combination of fear and exhilaration, he tried to pull on the green plastic surrounding the card slot and found that it peeled right off.
Three Skimmers Found in One Week
But that same week Nick McGlynn, a 26-year-old photographer, also spotted an ATM skimmer at a different Chase bank in New York City. He had just read about Seibel's experience on a technology blog, when he walked by a set of Chase ATMs that looked peculiar.
"From the window, I could see a mirror centered on one ATM but no mirror on another," he said.
E-Secure-IT
https://www.e-secure-it.com
After a fantastic week in Las Vegas at the ETA Show, we are scheduled to participate in FinovateStartup09 tomorrow. I depart Phoenix for San Francisco this morning to meet up with HomeATM CEO Ken Mages and COO, Mitch Cobrin who flew directly there from Las Vegas. It looks to be an exciting time and we look forward to meeting with several other providers of financial innovations whom were also invited to participate. We've got a filmed demo scheduled for this afternoon and then you can look for some sporadic coverage of FinovateStartUp09 during the course of the day tomorrow. For more information on FinovateStartup09, click the following link: www.finovate.com I've included a copy of our press release (below) announcing our participation which also provides more details about the event. Off to the airport!
HomeATM to Participate in FinovateStartup09
| HomeATM has been invited to to discuss themerits of their innovative Internet PIN Debit Solution atFinovateStartup09, to be held in San Francisco on April 28th. |
FOR IMMEDIATE RELEASE
PRLog (Press Release) – Apr 10, 2009 – Chicago: HomeATM is pleased to announce that itwill be participating at the FinovateStartup09 Conference, April 28, inSan Francisco, California. HomeATM CEO Ken Mages and COO Mitch Cobrin will be discussing thecompany's patented and PCI 2.0 Certifed Online PIN Debit Solution.
HomeATM engineered and now manufactures the World's First and OnlyPIN Entry Device designed specifically for eCommerce use. The PaymentCard Industry, which consists of representatives from Visa, MasterCard,American Express, Discover and JCB International, approved the devicelast month in a milestone event toward PIN Debit on the web becomingubiquitous. A majority of industry experts agree that a hardwareapproach towards PIN Debit for the web is the only way to secure andprotect valuable cardholder data from fraudsters.
"We are pleased to be able to demonstrate why a hardware approachto protecting cardholder data in a web based transaction is far moresecure than any other approach imaginable,"
The HomeATM PIN device plugs into any USB port in milliseconds andis Plug and Play...there is no software or drivers that need to beinstalled.
"When a consumer swipes their card using HomeATM's SafeTPIN, itresults in a "Card Present" transaction, which is not only a moresecure way to process bank cards, but provides the merchant withsignificantly lower Interchange fees," Frank explained. "By incorporating a PIN Pad into their device, merchants enjoy a duallyauthenticated transaction, which provides them with "true" PIN DebitInterchange as well."
"The value we can provide internet merchants is enhanced with our recent PCI 2.0 Certification,"
HomeATM's PCI 2.0 Certified SafeTPIN was also designed to be usedas an authentication device, replacing easily hacked Username/Password:
With the recent rash of breaches, it is important to provideconsumers and merchants with the most secure payment and authenticationmechanisms available. In the brick and mortar world, that mechanism isPIN Debit. HomeATM is poised to bring it to the other world...theworld wide web.
FinovateStartup is a spin-off of the New York City-based Finovateconference, the first demo-focused conference in financial technology.It is organized by Online Financial Innovations, a boutique bankingtechnology research firm based in Seattle, Washington.
Select companies will have seven minutes on stage for ademonstration of their best products or services. Some areas to becovered are: Person-to-person (P2P) lending, new marketing tools,better online financial security, mobile banking and payments, Web 2.0investing, personal finance, Online PIN Debit and next-generationonline banking platforms. FinovateStartup's debut last year had almost300 executives, entrepreneurs and industry experts in attendance.
In other news, HomeATM will also be at the ETA Meeting & ExpoApril 21-23 at the Mandalay Bay Resort & Casino in Las Vegas. Stopby and visit us at the FIS Booth #347 and get a FREE HomeATM PINDevice!
For more info please visit Fidelity National Information Services website: http://www.fismoreinfo.com/
About HomeATM:
HomeATM owns a global patent for secure Internet PIN basedtransactions. Leveraging our E2EE PCI 2.0 PED certified solution, amerchant or remitter can move funds from their bank account or openloop/closed loop payment card in real-time. Utilizing HomeATM'spatented solution with a bank issued card alleviates the burden formerchants to address fraud issues as HomeATM leverages the issuingbank's KYC/AML (Know Your Customer/Anti-
For further information, visit: http://HomeATMBlog.com or contact John B. Frank, Executive Advisor, jfrank@HomeATM.net or 612.432.6980
About Fidelity National Information Services
Fidelity National Information Services (FIS) is the world'stop-ranked technology provider to the banking industry. With more than24,000 experts in 90 countries, FIS delivers the most comprehensiverange of solutions for the broadest range of financial markets, allwith a singular focus: helping you succeed. Every FIS solution has thestrength you need for profitability today, and the power to help youmanage whatever comes next.
Recently FIS entered into an agreement to acquire Metavante, a leadingprovider of banking and payment technologies to financial servicesfirms and businesses worldwide. Metavante is based in Milwaukee,Wisconsin, with more than 5,900 employees and 8,000 clients worldwide.The combined company will be headquartered in Jacksonville, Florida,and will provide one of the most comprehensive ranges of integratedproducts and services, across more markets and more geographies thanany other provider in the industry.
For more information visit: www.PINDebit.blogspot.com
To View the Official Press Release, click here
 Is Google Targeting Facebook for a Hit?
Is Google Targeting Facebook for a Hit? Editor's Note: Based on conversations I've had with several people, the general consensus is that Facebook is teetering on the brink of "has been" land. Or should I say "tweetering?" For example, they certainly could use a person to person payment platform, yet recently announced they have killed that idea. I don't know what they are waiting for. (Maybe for a couple of their 20 somethings to hit 30 and be a little smarter)) Problem is...I don't know if they have the luxury waiting...
Here's an article which flat out states that Facebook is being "profiled" and will be "faced" by Google.
Google has a "Facebook killer" on its hands. And, no, I'm not talking about Google's Orkut social network (unless you live in Brazil, where Orkut has already "killed" Facebook).
Google is just one acquisition away from offering a social network that does everything Facebook does, minus all the things everybody hates about Facebook.
This social network is called Google Profiles.
You can choose a "vanity URL" of sorts, meaning you can use your Gmail address as part of your Google Profiles URL. (The URL used to use a long string of numbers.) For example, my new URL is: www.google.com/profiles/mike.elgan
Looking at it now, you'd never guess that Google Profiles is the biggest potential threat to Facebook anywhere. But Profiles is still missing one crucial ingredient. (Editor's Note: Can you say: "Twitter"?)
Read the full story
Source: News
Complete item: http://www.news.com.au/dailytelegraph/story/0,22049,25375352-5015795,00.html
GLOBAL banking and tax laws are a joke, says an Australian university researcher who used Google and $10,000 to establish a series of shell corporations which could easily have been used by criminal organizations to launder money.
Professor Jason Sharman, from Queensland's Griffith Business School, set up shell corporations and bank accounts without any identification. A shell company serves as a means for conveyance for business transactions without necessarily having assets.
He found it was banks in the US and UK which were flouting the rules, not the smaller island tax havens. In one case, he said, a US provider in Wyoming offered to use their own employees' social security numbers as the tax identification number for a corporation.
Prof Sharman set out to see how difficult it was to violate recent global standards stopping anonymous participation in the international financial system. He emailed 45 corporate service providers across 22 countries soliciting offers to set up anonymous shell corporations - and 17 agreed.
 Of these, 13 were from OECD countries, including seven in the United Kingdom, four in the United States, one in Spain, and one in Canada, and the remaining four from some of the 28 better known tax havens.
Of these, 13 were from OECD countries, including seven in the United Kingdom, four in the United States, one in Spain, and one in Canada, and the remaining four from some of the 28 better known tax havens.
E-Secure-IT
https://www.e-secure-it.com
Complete item: http://www.news.com.au/dailytelegraph/story/0,22049,25375352-5015795,00.html
GLOBAL banking and tax laws are a joke, says an Australian university researcher who used Google and $10,000 to establish a series of shell corporations which could easily have been used by criminal organizations to launder money.
Professor Jason Sharman, from Queensland's Griffith Business School, set up shell corporations and bank accounts without any identification. A shell company serves as a means for conveyance for business transactions without necessarily having assets.
He found it was banks in the US and UK which were flouting the rules, not the smaller island tax havens. In one case, he said, a US provider in Wyoming offered to use their own employees' social security numbers as the tax identification number for a corporation.
Prof Sharman set out to see how difficult it was to violate recent global standards stopping anonymous participation in the international financial system. He emailed 45 corporate service providers across 22 countries soliciting offers to set up anonymous shell corporations - and 17 agreed.
E-Secure-IT
https://www.e-secure-it.com
SONY LAUNCHES CONTACTLESS PAYMENTS TV REMOTE
Sony has launched a television remote control with a built in contactless reader that can be used to pay for watching on-demand content.
More on this story: http://www.finextra.com/fullstory.asp?id=19966
or go to Engadget to see more: http://www.engadget.com/tag/felica/
Sony has launched a television remote control with a built in contactless reader that can be used to pay for watching on-demand content.
More on this story: http://www.finextra.com/fullstory.asp?id=19966
or go to Engadget to see more: http://www.engadget.com/tag/felica/
By Ryan Blitstein - San Jose Mercury News
Somewhere in St. Petersburg, Russia’s second largest city, a tinystartup has struck Internet gold. Its dozen-odd employees are barelyold enough to recall the demise of the Soviet Union, but industryanalysts believe they’re raking in well over $100 million a year fromthe world’s largest banks, including Wells Fargo and Washington Mutual.
Their two-year rise might be the greatest success story of theformer Eastern Bloc’s high-tech boom — if only it weren’t so illegal.But the cash may be coming from your bank account, and they could beusing the computer in your den to commit their crimes.
The enigmatic company, which the security community has dubbed “RockPhish,” has rapidly grown into a giant of the Internet underground byperfecting a common form of Internet crime known as “phishing.” Thethieves capture people’s personal computers, then use them to sendphony e-mails that trick other users into revealing private financialinformation.
“Rock is the standard. They’re the Microsoft. Everyone else is a bitplayer,” said Jose Nazario, a researcher at security company ArborNetworks.
As big as Rock Phish has become, though, it is a sliver of a much larger problem.
During the past few years, a professional class bent on stealthyonline fraud has transformed Internet crime, rendering obsolete thehobbyist hackerswho sought fun and fame. These Al Capones of the information age arelike ghosts in our Web browsers, silently taking over our computers,stealing digital bits, and turning our data into cash. Take cyber-bite out of crime… Read the rest…
Editor's Note: Below are some of the more famous procerdures found lurking in the cybercriminal mind. When you realize that 93% of attacks target financial institutions, 92% target software applications and 90% are conducted by "organized crime" then add the fact that graphical user interfaces can be cloned, as can bank websites, the future of a software PIN debit application is behind the eight ball.
Vocabulary of cybercrime
Liketraditional crime, cybercrime can take many shapes and can occur nearlyanytime or anyplace. Criminals committing cybercrime use a number ofmethods, depending on their skill-set and their goal. This should notbe surprising: cybercrime is, after all, simply 'crime' with some sortof 'computer' or 'cyber' aspect.
The Council of Europe's Cybercrime Treaty uses the term'cybercrime' to refer to offenses ranging from criminal activityagainst data to content and copyright infringement [Krone, 2005].However, others [Zeviar-Geese, 1997-98] suggest that the definition isbroader, including activities such as fraud, unauthorized access, childpornography, and cyberstalking. The United Nations Manual on thePrevention and Control of Computer Related Crime includes fraud,forgery, and unauthorized access [United Nations, 1995] in itscybercrime definition.
As you can see from these definitions, cybercrime can cover avery wide range of attacks. Understanding this wide variation in typesof cybercrime is important as different types of cybercrime requiredifferent approaches to improving your computer safety.
Symantec draws from the many definitions of cybercrime and defines it concisely as any crime that is committed using a computer or network, or hardware device.The computer or device may be the agent of the crime, the facilitatorof the crime, or the target of the crime. The crime may take place onthe computer alone or in addition to other locations. The broad rangeof cybercrime can be better understood by dividing it into two overallcategories, defined for the purpose of this research as Type I and TypeII cybercrime.
Type I cybercrime has the following characteristics:
Examples of this type of cybercrime include but are not limited to phishing, theft or manipulation of data or services via hacking or viruses, identity theft, and bank or e-commerce fraud.
Type II cybercrime, at the other end of the spectrum,includes, but is not limited to activities such as cyberstalking andharassment, child predation, extortion, blackmail, stock marketmanipulation, complex corporate espionage, and planning or carrying outterrorist activities. The characteristics of Type II cybercrime are:
Somewhere in St. Petersburg, Russia’s second largest city, a tinystartup has struck Internet gold. Its dozen-odd employees are barelyold enough to recall the demise of the Soviet Union, but industryanalysts believe they’re raking in well over $100 million a year fromthe world’s largest banks, including Wells Fargo and Washington Mutual.
Their two-year rise might be the greatest success story of theformer Eastern Bloc’s high-tech boom — if only it weren’t so illegal.But the cash may be coming from your bank account, and they could beusing the computer in your den to commit their crimes.
The enigmatic company, which the security community has dubbed “RockPhish,” has rapidly grown into a giant of the Internet underground byperfecting a common form of Internet crime known as “phishing.” Thethieves capture people’s personal computers, then use them to sendphony e-mails that trick other users into revealing private financialinformation.
“Rock is the standard. They’re the Microsoft. Everyone else is a bitplayer,” said Jose Nazario, a researcher at security company ArborNetworks.
As big as Rock Phish has become, though, it is a sliver of a much larger problem.
During the past few years, a professional class bent on stealthyonline fraud has transformed Internet crime, rendering obsolete thehobbyist hackerswho sought fun and fame. These Al Capones of the information age arelike ghosts in our Web browsers, silently taking over our computers,stealing digital bits, and turning our data into cash. Take cyber-bite out of crime… Read the rest…
Editor's Note: Below are some of the more famous procerdures found lurking in the cybercriminal mind. When you realize that 93% of attacks target financial institutions, 92% target software applications and 90% are conducted by "organized crime" then add the fact that graphical user interfaces can be cloned, as can bank websites, the future of a software PIN debit application is behind the eight ball.
Vocabulary of cybercrime
- Bot-herders: Those who control the armies of computers known as botnets.
- Botnet: A “robot network,” or collection of zombie PCs, usually controlled by Internet crooks who have surreptitiously installed malware on people’s computers
- DNS Hijacking: Users type in a website and unbeknowst to them, they are taken to a cloned site whereby they enter their private information which is then used at the genuine website to log-in. Usually targeted at financial institutions.
- Drive-by download: A user visits a Web site containing malicious code that installs itself on the user’s PC.
- The Bad GUI: A cloned Graphical User Interface which replicates the genuine and fools user's into entering their valuable financial information like PIN's or Username's and Passwords. (see picture on right and below left)
- Keylogging: Software that records a user's keystrokes to steal passwords, usernames, credit card numbers, etc. (see picture below right)
- Malware: Any computer software created with malicious intent.
- Phishing: Sending e-mailsthat appear to come from a trusted entity (such as a bank or well-knowncompany) that trick people into giving up personal and financialinformation.
- Spam: Unwanted e-mails sent to users to get them to buy something, take an action or reveal information.
- Trojan: Malicious computer software disguised as a useful program that tricks users into opening or installing it.
- Virus: Computer code that infects a file or program, then takes actions and spreads when the user opens that file or program.
- Worm: A self-replicating computer program that transfers itself between PCs, often clogging the network as it spreads
- Zombies: What makes your financial information the walking dead...here's more on Cybercrime from Symantec:
Liketraditional crime, cybercrime can take many shapes and can occur nearlyanytime or anyplace. Criminals committing cybercrime use a number ofmethods, depending on their skill-set and their goal. This should notbe surprising: cybercrime is, after all, simply 'crime' with some sortof 'computer' or 'cyber' aspect.
The Council of Europe's Cybercrime Treaty uses the term'cybercrime' to refer to offenses ranging from criminal activityagainst data to content and copyright infringement [Krone, 2005].However, others [Zeviar-Geese, 1997-98] suggest that the definition isbroader, including activities such as fraud, unauthorized access, childpornography, and cyberstalking. The United Nations Manual on thePrevention and Control of Computer Related Crime includes fraud,forgery, and unauthorized access [United Nations, 1995] in itscybercrime definition.
As you can see from these definitions, cybercrime can cover avery wide range of attacks. Understanding this wide variation in typesof cybercrime is important as different types of cybercrime requiredifferent approaches to improving your computer safety.
Symantec draws from the many definitions of cybercrime and defines it concisely as any crime that is committed using a computer or network, or hardware device.The computer or device may be the agent of the crime, the facilitatorof the crime, or the target of the crime. The crime may take place onthe computer alone or in addition to other locations. The broad rangeof cybercrime can be better understood by dividing it into two overallcategories, defined for the purpose of this research as Type I and TypeII cybercrime.
Type I cybercrime has the following characteristics:
- It is generally a single event from the perspective of the victim.For example, the victim unknowingly downloads a Trojan horse whichinstalls a keystroke logger on his or her machine. Alternatively, thevictim might receive an e-mail containing what claims to be a link toknown entity, but in reality is a link to a hostile website.
- It is often facilitated by crimeware programs such as keystroke loggers, viruses, rootkits or Trojan horses.
- Softwareflaws or vulnerabilities often provide the foothold for the attacker.For example, criminals controlling a website may take advantage of avulnerability in a Web browser to place a Trojan horse on the victim'scomputer.
Examples of this type of cybercrime include but are not limited to phishing, theft or manipulation of data or services via hacking or viruses, identity theft, and bank or e-commerce fraud.
Type II cybercrime, at the other end of the spectrum,includes, but is not limited to activities such as cyberstalking andharassment, child predation, extortion, blackmail, stock marketmanipulation, complex corporate espionage, and planning or carrying outterrorist activities. The characteristics of Type II cybercrime are:
- It is generally an on-goingseries of events, involving repeated interactions with the target. Forexample, the target is contacted in a chat room by someone who, overtime, attempts to establish a relationship. Eventually, the criminalexploits the relationship to commit a crime. Or, members of a terroristcell or criminal organization may use hidden messages to communicate ina public forum to plan activities or discuss money launderinglocations, for example.
- It is generally facilitated by programs that do notfit into under the classification crimeware. For example, conversationsmay take place using IM (instant messaging) clients or files may betransferred using FTP.
Below is a link to a report titled "ATM Card Skimming and PIN capturing Awareness Guide". This document was put together by Commonwealth Bank in Australia. I've included four of the 20 slides, each of which you may click to enlarge.
Here's the First of the four slides:
 Here's yet "another" reason why banks should utilize HomeATM's SafeTPIN for authentication.
Here's yet "another" reason why banks should utilize HomeATM's SafeTPIN for authentication. SafeTPIN securely authenticates the user by allowing them to swipe their bank issued card and enter their bank issued PIN. No data other than the information contained on the magnetic stripe is collected so the privacy issue being discussed below is moot. End result?
Fraud elimination, consumer privacy protection AND it enables the online banking customer to securely pay bills, transfer money and conduct safe eCommerce transactions, all with 2FA, 3DES end to end encryption and DUKPT key management.
CAUTION: If your financial institution employs a "Username:/Password" style authentication, side effects from using our 2FA (two factor authentication) PCI 2.0 certified SafeTPIN PED may include: enhanced image for the bank, elimination of the threat of a cloned website, DNS attacks, malicious code, malware, keylogging, click jacking, worms and zombies. Be aware that Cloned cards won't work in our SafeTPIN and phishing attacks are useless. Pregnable transactions should not use SafeTPIN. Please consult with your technician!
 Device identification in online banking is privacy threat, expert says | Security - CNET News
Device identification in online banking is privacy threat, expert says | Security - CNET NewsSAN FRANCISCO--A widely used technology to authenticate users when they log in for online banking may help reduce fraud, but it does so at the expense of consumer privacy, a civil liberties attorney said during a panel at the RSA security conference on Thursday.
When logging into bank Web sites, users are typically asked for their user name and password. But that's not all that is happening. Behind the scenes, the server is taking measures to identify the device being used in an attempt to verify that the person logging in is the person whose account is being accessed under the assumption that most people use the same computer for banking.
Wachovia, which recently merged with Wells Fargo, tags the consumer's computer with a unique identifier, said Chris Mathes, an information technology specialist in online customer protection at the bank.
The technology not only can be used to allow legitimate customers into Web sites, but also to block computers that have been targeted as "bad actors," said Todd Inskeep, a senior vice president for the Center for the Future of Banking at Bank of America.
Even though none of the information gathered during a log-in is personally identifiable, the bank shouldn't have to collect regular data on when, how often and from where a consumer accesses a bank account, said Jennifer Granick of the Electronic Frontier Foundation. Such information can be compiled with other more sensitive information to create profiles and cross referenced to learn more about consumers, she said.
For instance, the bank could learn who a consumer's roommate is if the same computer is used regularly to access different accounts, Granick said. Consumers also could be deemed suspicious for breaking with their patterns on deposits or withdrawals or the information could be sold to advertisers, she added.
Continue Reading at CNET
| |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Powered by Blogger.